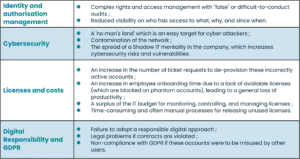
The proliferation of these accounts is due mainly to incomplete or non-existent management of the identity life cycle, which impacts the access and authorization lifecycle.
A direct link between the status of identity and the automatic calculation of resource allocation, backed up by frequent synchronization with the target systems, allows this holistic and comprehensive vision and governance to contain the emergence of orphan accounts at the source. An Identity and Access Management (IAM) solution with a flexible and structured architecture makes it possible to easily cover all joiners, movers & leavers within the organization, whether it is: